When Is Parallelism Fearless and Zero-Cost with Rust?
Today’s Issue: C to Rust Code Translator, Will Rust Survive the Next Decade? And uuid Crate Now Properly Supports Version 7 Counters
Happy end of the month, Rustaceans!
Welcome to another edition of the Rust Bytes newsletter. In this issue, we’ll highlight a research paper “When Is Parallelism Fearless and Zero-Cost with Rust?”, present a Rust challenge, spotlight an amazing Rust project, and highlight some incredible links of the week.
Welcome to issue 38.
THE MAIN THING
When Is Parallelism Fearless and Zero-Cost with Rust?
The fantastic five: Javad Abdi, Gilead Posluns, Guozheng Zhang, Boxuan Wang, and Mark C. Jeffrey, released a research paper that has been the talk of the week.
Their research paper titled “When Is Parallelism Fearless and Zero-Cost with Rust?” investigates whether Rust lives up to its claim of enabling "fearless concurrency with zero cost" for parallel programming.
The study involved analysis of 14 benchmarks ported from C++ to Rust, covering both regular and irregular parallelism. The researchers used the Rayon library for parallel constructs and evaluated the ease and safety of expressing parallelism in Rust.
This thoroughly researched paper found that while Rust excels at handling regular parallelism, it struggles with irregular parallelism, leaving rustaceans with the same challenges as other languages.
Here are some key findings from the study:
Regular Parallelism. Rust's type system excels at catching concurrency errors at compile time for programs with regular data access patterns (e.g., parallel prefix sums). This makes parallel programming "fearless" in these cases.
Irregular Parallelism. When tasks have irregular access patterns to shared data (e.g., modifying elements in a hash table concurrently), Rust requires either unsafe code (risky) or synchronization primitives (overhead and potential for errors). This makes parallel programming "scary" again.
Synchronization. While Rust enforces data races by requiring synchronization, it doesn't eliminate other synchronization errors like deadlocks or livelocks. Programmers still need to be cautious of such scenarios.
Performance. Rust's benchmarks were generally slower than their C++ counterparts, but the gap was not significant.
The paper also introduces a "fear spectrum" to categorize the level of fear associated with parallel programming in Rust.
Fearless. Errors are caught at compile time.
Comfortable. Errors are caught at runtime with clear diagnostics.
Scared. Errors might go undetected, leading to non-deterministic behavior.
The research found that while Rust offers significant advantages for regular parallelism, it falls short for irregular cases. Rustaceans need to carefully consider the trade-offs between safety and performance when using Rust for parallel programming tasks.
For a deeper dive, please refer to the full paper available here.
RUST CHALLENGE❓
In our previous issue you were tasked with implementing the GA-DE-RY-PO-LU-KI cypher. Here is our solution for the challenge. Are their better ways to solve the challenge? We would love to hear your solution.
Here is a Challenge for you.
Crack the PIN
DESCRIPTION:
Given is a md5 hash of a five digits long PIN. It is given as string. Md5 is a function to hash your password: "password123" ===> "482c811da5d5b4bc6d497ffa98491e38"
Why is this useful? Hash functions like md5 can create a hash from string in a short time and it is impossible to find out the password, if you only got the hash. The only way is cracking it, means try every combination, hash it and compare it with the hash you want to crack. (There are also other ways of attacking md5 but that's another story) Every Website and OS is storing their passwords as hashes, so if a hacker gets access to the database, he can do nothing, as long the password is safe enough.
Note: Many languages have build in tools to hash md5. If not, you can write your own md5 function or google for an example.
Your task is to return the cracked PIN as string.
This is a little fun kata, to show you, how weak PINs are and how important a bruteforce protection is, if you create your own login.
You can share your solution with us or the code snippet on Rust Playground. Enjoy!
PROJECT SPOTLIGHT 💡
C2Rust
Our Project Spotlight this week shines a light on a transformation so sweet, it'll make even the most jaded city dweller believe in happy endings.
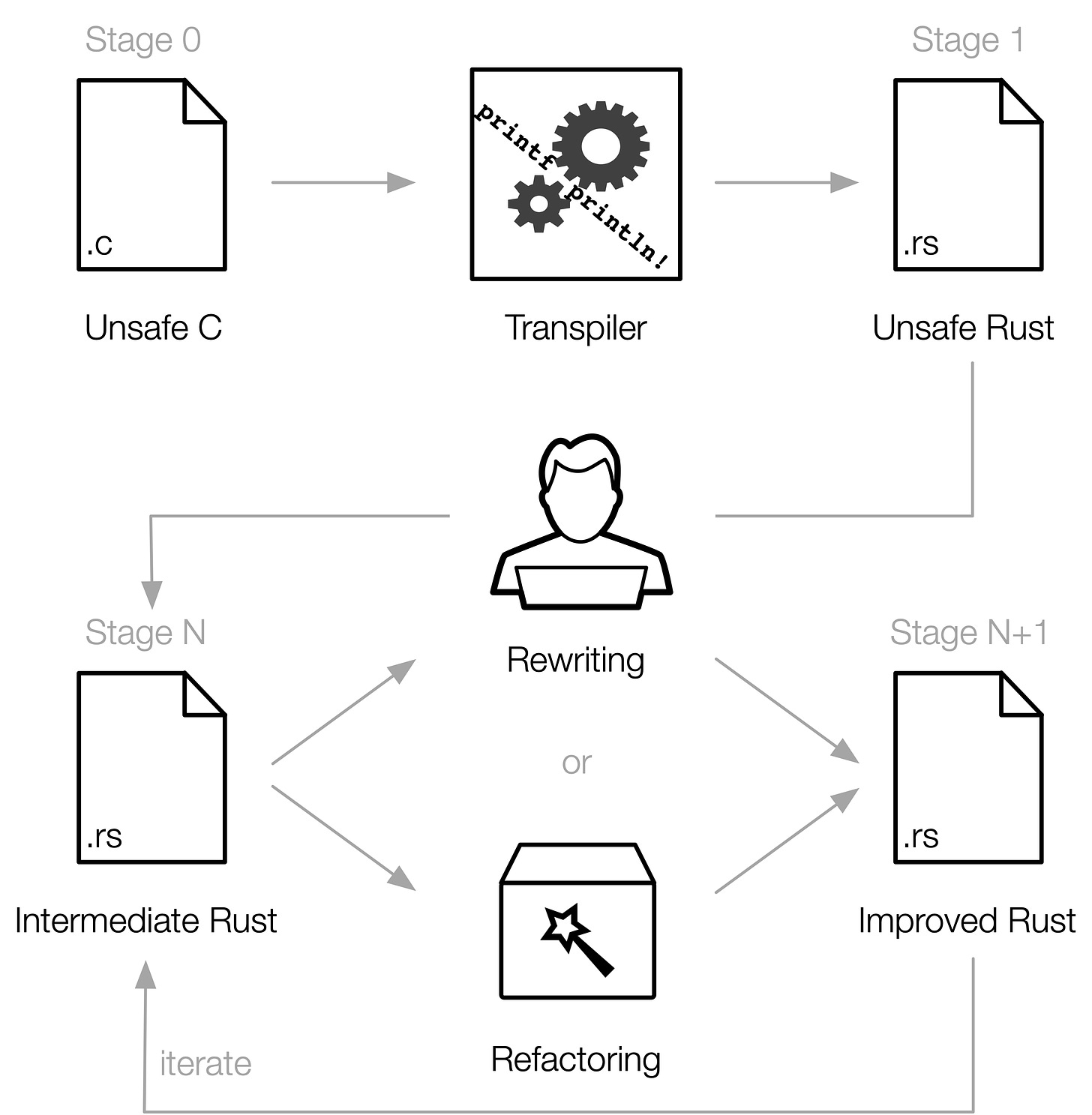
C2Rust helps you migrate C99-compliant code to Rust. The translator (or transpiler), c2rust transpile, produces unsafe Rust code that closely mirrors the input C code. The primary goal of the translator is to preserve functionality; test suites should continue to pass after translation.
What C2Rust has to offer:
C2Rust translates your C code into Rust code, aiming to preserve functionality.
The translated Rust code is designed to be memory-safe, helping to prevent crashes and security vulnerabilities.
C2Rust analyzes your C code to understand its structure and functionality.
While not fully there yet, C2Rust aims to eventually support translating code for different platforms. Currently, cross-compilation of translated code is not supported.
And if that’s not all, C2Rust is open-source on Github.
AWESOME LINKS OF THE WEEK 🔗
The Rust Types Team blogged about Types Team Update and Roadmap.
Building in Rust just got a whole lot smoother, AWS CodeArtifact now supports Cargo, the Rust package manager.
Rust Ukraine 2024 CFP is on, submit your speaker talk and join an epic dev gathering. Applications close on July 6th ⏳
Will Rust survive the next decade? Hugo from Tweede Golf asks the question on everyone's mind!
Orhun Parmaksız released git-cliff 2.4.0.
Luca Palmieri spilled the beans on Pavex and other delightful dev topics with Drew in an interview that was more lit than a Friday night deploy.
Uuid crate now properly supports version 7 counters.
Who knew learning Rust could be gamified? Jonathan Österberg's Kartoffels lets you game your way to Rust programming mastery.
Mahor Foruzesh released reddish-shift - A port of jonls/redshift to Rust.
David wrote a tutorial on Implementing JSON parsing in Rust. It’s too good we promise.
Do you have a challenging Rust problem/Tip you'd like to share with fellow Rustaceans? We'd be more than happy to feature them in a future issue, with full credit given to you. Submit your challenges or tips to us via email rustaceanseditors@gmail.com.
BEFORE YOU GO 👋
You're our biggest fans, and we love to see it. Here are a few ways you can help us spread the word:
❤️ Recommend Rust Bytes to your friends.
🤳 Connect with us on our socials: X, Rustaceans Publication.
📨 Contact us through rustaceanseditors@gmail.com feedback is welcome.
☕️ Buy Us Coffee.
That's all for now, Rustaceans. Wishing you the best of the new month.
John & Elley.